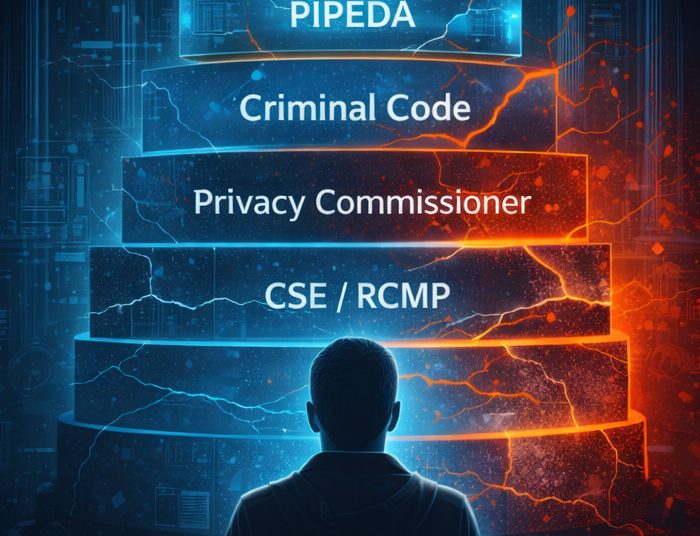
When Canadians hear the term cyber law, many assume it’s a single, clear set of rules designed to protect them online. In reality, cyber law in Canada is a patchwork of laws, regulators, and agencies — each responsible for a specific slice of the digital world. Understanding who does what is the first step to understanding where protection exists, and where it doesn’t.
Let’s start at the top.
The Top-Level Federal Law: Privacy and Data Protection
At the federal level, the most important cyber-related law affecting everyday Canadians is PIPEDA – the Personal Information Protection and Electronic Documents Act. In simple terms, PIPEDA governs how private-sector organizations collect, use, and store personal information in the course of commercial activities. If a company operates across provincial borders, or online, PIPEDA almost certainly applies.
PIPEDA is built on a few basic principles:
- Companies must have a reason to collect your data
- They should only collect what they need
- They must protect it
- They should tell you what they’re doing with it
- You have the right to access and correct it
That’s the theory. Enforcement is another story.
What Falls Under PIPEDA?
Under PIPEDA, “personal information” is defined broadly. It includes:
- Names, email addresses, phone numbers
- Financial and billing data
- Health and genetic information
- IP addresses and online identifiers (in many cases)
If a company loses this data in a breach, it must:
- Assess the risk of harm
- Notify affected individuals if there is “real risk of significant harm”
- Report serious breaches to the Privacy Commissioner
However, PIPEDA does not directly punish companies. This is a key limitation many Canadians don’t realize.
The Privacy Commissioner of Canada: Oversight, Not Enforcement
The Office of the Privacy Commissioner of Canada (OPC) is the main federal privacy regulator. Its job is to:
- Investigate complaints from individuals
- Audit organizations
- Make findings and recommendations
- Educate the public
What it cannot currently do (under PIPEDA):
- Issue fines on its own
- Order companies to change practices immediately
- Force compensation
The OPC functions more like a watchdog and ombudsman than a police force. It can publicly shame, pressure, and recommend – but enforcement is limited.
This is one reason Canada has been pushing for reform through Bill C-27, which would introduce stronger enforcement powers and penalties. Until that happens, protection remains largely reactive.
Criminal Law: When Cyber Issues Become Crimes
Cyber law isn’t only about privacy. When activities cross into criminal territory – hacking, fraud, ransomware – the Criminal Code of Canada applies.
This is where law enforcement comes in.
NC3 and Law Enforcement: Chasing the Criminals
The Canadian Centre for Cyber Security (Cyber Centre), part of the Communications Security Establishment (CSE), focuses on defensive cybersecurity. It:
- Protects federal government systems
- Advises critical infrastructure (energy, telecom, finance)
- Issues alerts and guidance
It does not investigate individual crimes or help victims directly.
That role belongs to the National Cybercrime Coordination Centre (NC3), run by the RCMP. NC3 role is to:
- Collects cybercrime reports from Canadians
- Coordinates investigations across police forces
- Works with international partners
Important to understand: NC3 coordinates – it does not guarantee investigation. Many reports help with intelligence gathering rather than immediate action.

Provincial Layers: Even More Complexity
On top of federal law, provinces may have:
- Their own privacy laws (e.g., Quebec’s Law 25, Alberta and BC private-sector acts)
- Provincial privacy commissioners
- Provincial breach notification rules
Depending on where you live and which organization holds your data, different laws may apply.
The Big Picture: Why This Feels Confusing
Cyber law in Canada isn’t broken because people don’t care – it’s fragmented because it evolved piecemeal.
In plain English:
- Privacy law governs how companies should handle your data
- Privacy commissioners oversee and investigate
- Police handle crimes after damage is done
- Cybersecurity agencies focus on protecting systems, not people
There is no single authority “in charge of protecting Canadians online.” Understanding this structure doesn’t solve the problem – but it does explain why, when a breach happens, accountability often feels slow, distant, or incomplete. And that’s exactly why cyber law and policy deserve closer scrutiny.
SIDEBAR
Why This Matters to Canadians
When a data breach happens, many Canadians instinctively ask: Who is protecting me? The uncomfortable answer is: no single entity is fully responsible.
Canada’s cyber law framework was built to guide organizations, not aggressively police them. Privacy commissioners can investigate, but often cannot fine. Police can act, but usually only after harm occurs. Cybersecurity agencies protect systems, not individuals.
This matters because once your personal data is exposed, it cannot be “put back.” Credit monitoring expires. Settlements are symbolic. The long-term risk — identity theft, fraud, surveillance – stays with the individual.
Understanding how cyber law is structured helps Canadians see why accountability feels limited, why breaches keep happening, and why stronger enforcement is not a technical issue – it’s a policy choice.